What Type of Access Control List Defines the Settings for Auditing Access to an Object?
Affiliate vii
Object Access Events
Y'all can utilize the Object Access Security log category to audit whatsoever and all attempts to admission files and other Windows objects. In addition to tracking files, you tin can rails Success and Failure access attempts on folders, services, registry keys, and printer objects. The just auditable objects non covered by this category are AD objects, which you can track by using the Directory Service Access category.
The way in which you define the Audit object access policy and the format of information that the Security log records for this category are closely related to the structure of the Access Control Lists (ACLs) that all objects utilize to define who can access the object and how. When you lot enable the Inspect object admission policy for a given computer, Windows doesn't immediately begin auditing all Object Access events for all objects; if it did so, the system would immediately grind to a halt.
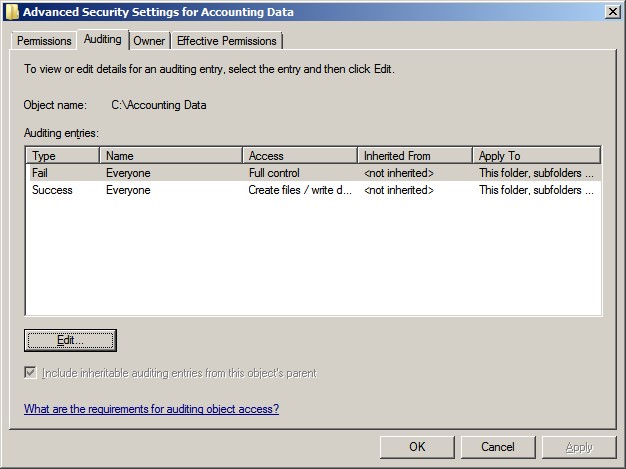
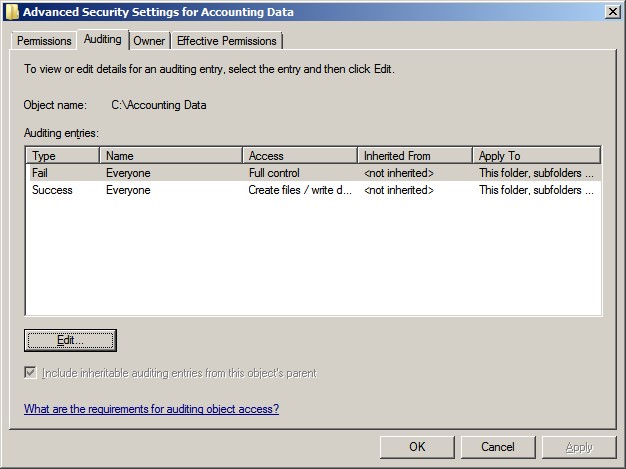
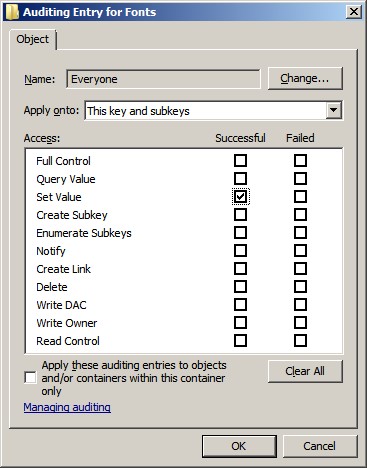
Activating Object Admission auditing is a ii-step process. First, enable the Audit object admission policy on the system that contains the objects that you lot want to monitor. Second, select specific objects and ascertain the types of access y'all want to monitor. Make these selections in the object'southward inspect settings, which you'll observe in the object's Advanced Security Settings dialog box shown beneath.
Object Access has 11 subcategories. The two primary subcategories are File Organisation and Registry, which rails access events for the file organization and registry, respectively.
| Object Access Subcategories | Comment |
| File System | Track files and folders. |
| Registry | Runway access to registry keys and values. |
| Kernel Object | Nosotros did not observe whatsoever events associated with this subcategory. |
| SAM | Rail objects in the local Security Account Manager. |
| Certification Services | Built-in Certificate Potency and PKI-related events. |
| Awarding Generated | Awarding reports events to Security log. |
| Handle Manipulation | Nosotros presently classify these events as noise. |
| File Share | Logs the first time a share is accessed. |
| Filtering Platform Packet Drib | Shows packets blocked past firewall and filtering platform. |
| Filtering Platform Connectedness | Shows applications and connections immune or denied by filtering. |
| Other Object Access Events | Miscellaneous object events include Scheduled Tasks, DNS, and Plug&Play. |
2 other types of objects—Kernel and SAM objects—have their own subcategories, which will be discussed subsequently in this chapter. Finally, whatsoever remaining object types (e.g., services) that are not covered by specific subcategories are reported in the Other Object Access Events subcategory.
Note that all five of these categories share the aforementioned result IDs for object open, admission, close, and delete events. Therefore, it's of import that you lot filter events based not just on effect ID but on subcategory every bit well. Object Access events are 1 of the few Security log areas in which more than i subcategory tin generate an consequence ID. Additional subcategories address other areas of security activeness, including Windows Firewall events and Document Services.
| Consequence ID | Title |
| 4656 | A handle to an object was requested |
| 4658 | The handle to an object was closed |
| 4660 | An object was deleted |
| 4663 | An attempt was made to access an object |
Object Access Auditing
Using the "Avant-garde Security Settings" dialog box in the screenshot above y'all can limit auditing according to the user or group that is accessing the object (the Name column), the permissions that are requested (the Access column), and whether the access endeavor failed or was successful (the Type column). Windows evaluates an object'south inspect policy much as it evaluates the object's permissions. When a user attempts to access an object (eastward.g., when Fred tries to open budget.xls), Windows determines whether to report the attempt to the Security log. Windows analyzes all the audit entries that apply to the user who is attempting to access the object. If the object'south audit policy contains entries for several groups, and if the user who is attempting to admission the object belongs to two or more of those groups, and so Windows will log the event if whatever of the applicable entries match (i.e., if the user requested one or more of the permissions that are flagged for auditing and the consequence of the attempt matches the Success or Failure criteria of the inspect entry).
Suppose that Alice has Change access to the Accounting Data binder and its files, which include upkeep.xls. Write Data is amidst the permissions that Change access comprises. Alice uses Excel to open and write to upkeep.xls. Windows matches Alice's action to the second entry in the folder's Object Access inspect policy. Alice is a fellow member of the Everyone grouping, her permissions to the accessed file include Write Data, and her attempt to write to the file was successful. Windows would not match an attempt by Alice to open the file but to view it: Such an attempt would successfully use Read Data permissions, which aren't specified for auditing. Now suppose that Fred, who has no admission to Accounting Data, is snooping effectually the network and attempts to list the files in Accounting Data. Windows matches this failed access attempt to the first entry in the folder'due south inspect policy and trigger an Object Access outcome in the Security log.
The table below provides a complete list of permissions, the corresponding names used by Object Admission events in the Security log, and an explanation the permission as applied to folders and files.
| Permission | Name in Object Access Events | Explanation | |
| Binder | File | ||
| Traverse Folder/Execute File | Execute/Traverse | Binder traversed while browsing file organisation; permits movement through folders to reach other files or folders, if the user has no other permissions to the folders being traversed; has no issue unless the user lacks the Featherbed traverse checking user right, which is assigned to Anybody by default | Script or .exe file executed |
| List Folder/Read Data | ReadData (or ListDirectory) | Names of subfolders and files queried by Explorer, dir control, or application | Actual content of file read |
| Read Attributes | ReadAttributes | Attributes (Read Only, Archive, Arrangement, Hidden) queried by Explorer, attrib control, or application | |
| Read Extended Attributes | ReadEA | Extended attributes (as defined past applications) queried by Explorer, attrib command, or awarding | |
| Create Files/Write Data | WriteData (or AddFile) | New file created in the folder | Content of file changed |
| Create Folders/Append Information | AppendData (or AddSubdirectory or CreatePipeInstance) | New subfolder created in the folder | Content appended to end of file |
| Write Attributes | WriteAttributes | Attributes (Read Only, Archive, Arrangement, Hidden) modified past Explorer, attrib control, or awarding | |
| Write Extended Attributes | WriteEA | Extended attributes (equally defined by applications) modified by Explorer, attrib control, or awarding | |
| Delete Subfolders and Files | DELETE | Object deleted; allows or denies deletion of subfolders and files even when the user lacks Delete permission on the specific subfolder or file | |
| Delete | DELETE | Object deleted; overridden past Delete Subfolders and Files permission on the parent binder | |
| Read Permissions | READ_CONTROL | Object'southward ACL queried | |
| Modify Permissions | WRITE_DAC | Object'south ACL modified | |
| Take Ownership | SeTakeOwnershipPrivilege | Owner of object changed | |
Although you tin can limit auditing for a given object to specific groups or even individual users, we recommend sticking with the Everyone grouping. Singling out specific groups or users for monitoring puts you lot at risk of creating an incomplete audit trail and might expose y'all to claims of unfairness or raise questions as to the integrity of your data. Likewise be careful when specifying the type of access to monitor and when choosing whether to audit for Success or Fail types. You lot tin can easily create also inclusive an audit policy and drench the Security log with useless noise. In particular, think twice about enabling Success auditing of Read Data, Read Attributes, Prepare Extended Attributes, Read Permissions, and Execute permissions, which legitimate users use and then often during the course of work.
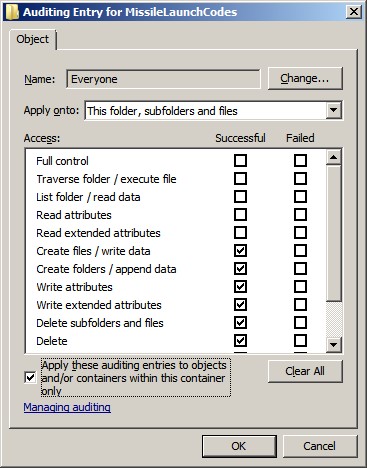
In improver to the Type, Name, and Access columns, an object'southward Advanced Security Settings comprise an Apply To column. Yous can specify values for this cavalcade for container objects such as folders, thereby controlling whether and how Windows propagates the audit entry to child objects. The Apply To value defaults to This binder, subfolders and files but can be changed to whatever combination of the three. You tin use the Apply To setting to fine-tune your inspect policy then that it ignores file or binder access events that are irrelevant to your audit needs, thus eliminating some noise from the Security log. For example, you might need a tape of who is accessing sensitive files in a certain folder but have no interest in folder-level admission, such every bit folder listings or creation of subfolders and files. In that instance, you lot can enable auditing for the appropriate permissions but change the Utilize To value to Files but. If yous'd like to restrict the behavior of Apply To to kid objects just prevent an audit entry from propagating to grandchild objects, you can select the Utilise these auditing entries to objects and/or containers within this container only check box.
To properly utilise the Utilize To setting, you must empathise the dual meaning of certain permissions. Note that some auditable permissions have a different pregnant for files than for folders. For instance, Create Folders/Append Data for a binder means that the user can create new subfolders inside the folder; for a file, the permission means that the user can append data to the end of the file. Likewise, List Binder/Read Data for a folder lets users only listing the names of files and subfolders within the folder; for a file, the permission lets users read the actual data contents of the file. What if you want to audit one of these dual meaning permissions for the folder only, not for the files inside the binder? Or what if you need to audit access to the files within the folder but not access attempts to the binder itself? In such cases, employ the Apply To setting.
When viewing an object's inspect policy, you can determine where each audit entry is defined by consulting the read-merely Inherited From column. In the case beneath, both entries are explicitly defined on the firsthand folder, so this column reads <not inherited>. If you need to break the menses of inherited permissions at a sure level in your folder hierarchy and block those permissions from propagating down to a detail subfolder, y'all can articulate the Include inheritable auditing entries from this object's parent check box.
Object auditing is basically the selective logging of the access control decisions that Windows makes. Earlier enabling and configuring an object's Object Access audit policy, know exactly what you mean to accomplish. Several mutual audit goals have corresponding audit settings.
| Goal | Inspect Settings | |
| Type | Access | |
| Audit trail of changes to a file | Success | Write Data Suspend Information |
| Know when someone tries to access an object that they shouldn't | Failure | All Permissions |
| Audit trail of admission command changes to a folder | Success | Change Permission |
| Inspect trail of deletion of a folder or of any file in the folder | Success | Delete Subfolders and Files Delete |
Operation-Based Auditing
Event ID 4656 logs the permissions that are requested by the application that'south trying to open a handle to the audited object. Only that doesn't hateful that the awarding actually exercised those permissions earlier closing the object. For example, a user might successfully open up an object for Read and Write admission but close the file without every changing its content.
In Windows, subsequently a user successfully opens a handle to an object and so exercises one or more than permissions, Windows logs result ID 4663. This effect, which is a big improvement over earlier methods, lists the Handle ID that was originally logged by event ID 4656, as well as the exercised permissions. Any subsequent uses of the same permissions do not trigger indistinguishable instances of event ID 4663; Windows simply logs event ID 4663 the outset fourth dimension that the user exercises a given permission betwixt the opening and endmost of the object. (Event IDs 4656 and 4658 are still necessary to prove when the object was open and when it was closed.)
Nosotros aren't sure why the outcome ID 4663 description specifies "access attempted." This event is always a Success event and shows the permission that was actually used.
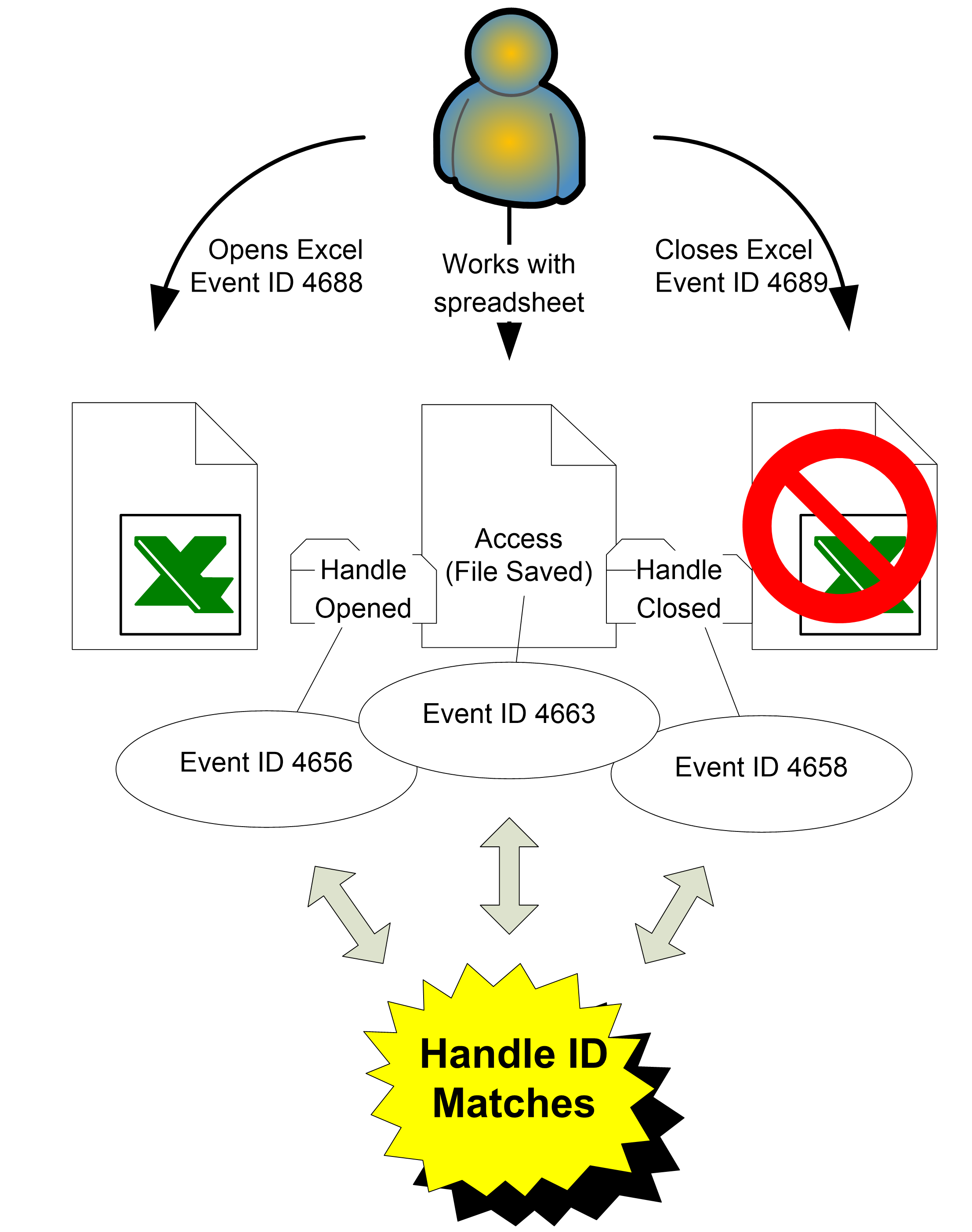
Windows handles object deletions a picayune differently than it handles other Object Admission events. In improver to logging result ID 4656, Windows logs outcome ID 4660 (Object Deleted), which lists the Handle ID that was originated in event ID 4656. When successful Delete access has been enabled for auditing on an object, Windows logs effect ID 4660 when that object is deleted. To determine the proper noun of the deleted object, y'all must correlate the Handle ID with other events (i.e., event IDs 4656, 4663, and 4658). Outcome 4660 will be in shut proximity to these events, but be enlightened that a process can open up an object for Delete access much earlier than the procedure really deletes the object.
It would exist easier if Windows logged the object's proper noun in instances of event ID 4660 (Object Delete), but you must connect result ID 4656 and the subsequent event ID 4660 by using the Handle ID field. Such multiple-event correlation or pattern recognition is beyond the ability of most current event-log software, simply we expect that to change as interest in the Security log continues to increase. Microsoft is getting ameliorate at providing information in the bodily events as they occur only a need to see a pattern will always remain.
Sometimes, when you install new updates to Windows, the installer is unable to replace existing files because they are in utilize by the operating system. The mutual arroyo in such situations is to instruct NTFS to delete the object the side by side time the organisation boots but before the file is put into use. Windows should log such deferred deletions in event ID 4659 (A handle to an object was requested with intent to delete). Microsoft documentation describes this event as an attempt to open an object with the intent to delete it. Note: Issue ID 4659 is used by file systems when the FILE_DELETE_ON_CLOSE flag is specified in Createfile(). This flag is the only way to delete files that were opened exclusively by another programme. However, as of the appointment of this publication, we accept not been able to produce this issue.
File Organisation
The File System subcategory tracks access to file organization objects. To ready SACLs for file arrangement objects in Windows Explorer, correct-click the file or folder object, choose Properties, Security tab, click Advanced, and go to the Auditing tab to access the object'southward Advanced Security Settings. Click Edit to change the auditing or run across the details.
| Issue ID | Championship |
| 4656 | A handle to an object was requested |
| 4658 | The handle to an object was closed |
| 4660 | An object was deleted |
| 4663 | An endeavor was fabricated to admission an object |
| 4685 | The state of a transaction has changed |
| 4985 | The state of a transaction has changed |
The Logon/Logoff and Detailed Tracking categories provide both an initialization and termination event ID that correspond to the showtime and end of a logon session or process. Likewise, the Object Access category generates event ID 4656 (Handle to object requested) when an object is opened and issue ID 4658 (Handle to object airtight) when the object is closed, along with other events in betwixt, depending on what the application does with the open object. These events' Handle ID description field serves the aforementioned purpose as the Logon ID and Process ID fields in Logon/Logoff and Detailed Tracking events. To determine how long a file was open, simply look for an instance of event ID 4658 that has the same Handle ID as the preceding event ID 4656.
Object Admission events reflect the interaction between Windows and an awarding—non betwixt a user and the application. For instance, when Carol uses Microsoft Word to open memo.physician, edits a paragraph, and and so closes the file, you might expect to find an instance of event ID 4556 followed by event ID 4658. Actually, unbeknownst to Ballad, Discussion opens and closes the file multiple times in connection with her deportment, and yous'll observe events reflecting all this activity. In addition, Word creates a 2d, temporary file while a document is open. This file is saved periodically and acts as a fill-in while the file is existence edited. Under normal conditions information technology is deleted when the file is closed. However, it may remain if a system crashes and Carol is unable to save it. When the file is opened again in Discussion the program allows Ballad to cull which document she wants to save.
The fact that Object Access events reflect lower-level, application-to-operating system activity doesn't render the category useless, only it means that the category generates many more than events than you might expect or want, making analysis more than complex. Some objects (east.1000., files) are never kept open for very long. Operations such as listing a binder or deleting a file or binder are single, atomic actions—but they still generate the open up and close instances of upshot ID 4656 and event ID 4658 in the Security log. Result ID 4656 provides many description fields that cover the object accessed, the user and plan involved, and the permissions requested. This event is a big improvement over the Windows Server 2003 Object Open up consequence 560. In Windows Server 2008 and later, the subject fields eliminate having to expect in two different places for which business relationship was used.
| Field | Caption |
| Subject | The user and logon session that performed the activeness |
| Security ID | The SID of the account |
| Business relationship Name | The account logon name |
| Account Domain | The domain proper noun or—in the example of local accounts—calculator name |
| Login ID | A number that is unique between reboots and that identifies the logon session |
| Object | The object upon which the action was attempted |
| Object Server | Always "Security" |
| Object Blazon | "File" for file or binder, only tin be other types of objects (e.g., Key, SAM, SERVICE OBJECT) |
| Object Name | The name of the object beingness accessed |
| Handle ID | A number that is unique between reboots and that allows you to correlate other events (i.due east., effect IDs 4656, 4658, and 4663) |
| Procedure Information | The procedure that Windows uses to admission the object |
| Process ID | The procedure that is specified when the executable started, as logged in event ID 4688 |
| Process Name | The program name and path |
| Access Request information | Information that is requested at the time the object is accessed; some programs asking more access than will actually exist used |
| Transaction ID | Employ unknown |
| Accesses | The permissions that are requested |
| Admission Mask | The bitwise equivalent of Accesses |
| Privileges used for Access Cheque | Privilege used to gain access (e.1000., SeTakeOwnershipPrivilege) |
This event's Procedure Proper name field identifies the total path name of the executable that was started. For instance, if a user opens Notepad, the upshot will show something like to C:\Windows\System32\notepad.exe as the process name. To uniquely identify each process during a system boot session, Windows uses a Process ID. Consequence ID 4688 (as discussed in Chapter half dozen) also lists the process ID of a new process in the New Procedure ID field and the Creator Procedure ID field.
At present that you understand the File System subcategory, let'south look at some Object Access auditing events from the other ten subcategories. Many events are duplicated in several subcategories.
Registry
When Object Access auditing is enabled, the Registry subcategory is enabled past default. You can also use Auditpol to prepare the subcategory auditing individually. To fix the SACL, open Regedit, correct-click the object, cull Permissions, click Avant-garde, and go to the Auditing tab.
Many of this subcategory's events are also logged by the File System subcategory. In improver, the new outcome ID 4657 documents creation, modification, and deletion of registry values. This event is logged betwixt event IDs 4656 (open) and 4658 (close) events for the registry key in which the value resides. See the Performance Blazon field in event ID 4657 to find out whether the value was created, modified, or deleted.
| Outcome ID | Championship |
| 4656 | A handle to an object was requested |
| 4657 | A registry value was modified |
| 4658 | The handle to an object was airtight |
| 4660 | An object was deleted |
| 4663 | An attempt was made to admission an object |
A big plus to this new consequence: it too tells y'all the old type/value prior to modification. Some possible types are listed in the chart below.
| Blazon | Explanation |
| REG_SZ | String value |
| REG_BINARY | Binary value |
| REG_DWORD | Double discussion 32-bit value |
| REG_QWORD | Quad discussion 64-bit value |
| REG_MULTI_SZ | Multi-string value |
| REG_EXPAND_SZ | Expandable cord value |
Kernel Object
Auditing events in the Kernel Object subcategory are probably of interest merely to developers. An case of a kernel object is a security token.
| Event ID | Title |
| 4658 | The handle to an object was airtight |
| 4660 | An object was deleted |
| 4661 | A handle to an object was requested |
| 4663 | An attempt was made to access an object |
SAM
Events in the SAM subcategory allow yous to rails admission to objects in the SAM in which local users and groups are stored on non-DC systems.
| Outcome ID | Title |
| 4658 | The handle to an object was closed |
| 4660 | An object was deleted |
| 4661 | A handle to an object was requested |
| 4663 | An attempt was made to access an object |
Certification Services
Certificate Services is the built-in Certification Authority and related Public Key Infrastructure (PKI) functionality in Windows Server. The Certifications Services subcategory events provide exhaustive auditing of related activity.
| Event ID | Title |
| 4868 | The certificate manager denied a pending certificate request. |
| 4869 | Document Services received a resubmitted certificate asking. |
| 4870 | Document Services revoked a certificate. |
| 4871 | Document Services received a request to publish the document revocation list (CRL). |
| 4872 | Certificate Services published the document revocation listing (CRL). |
| 4873 | A document request extension changed. |
| 4875 | Certificate Services received a request to close downward. |
| 4876 | Certificate Services backup started. |
| 4877 | Certificate Services backup completed. |
| 4878 | Certificate Services restore started. |
| 4879 | Certificate Services restore completed. |
| 4880 | Certificate Services started. |
| 4881 | Document Services stopped. |
| 4882 | The security permissions for Certificate Services changed. |
| 4883 | Certificate Services retrieved an archived primal. |
| 4884 | Document Services imported a document into its database. |
| 4885 | The audit filter for Document Services changed. |
| 4886 | Document Services received a certificate request. |
| 4887 | Certificate Services approved a certificate asking and issued a certificate. |
| 4888 | Certificate Services denied a document request. |
| 4889 | Certificate Services fix the status of a document request to pending. |
| 4890 | The certificate manager settings for Certificate Services changed. |
| 4891 | A configuration entry changed in Document Services. |
| 4892 | A property of Document Services changed. |
| 4893 | Certificate Services archived a key. |
| 4894 | Certificate Services imported and archived a key. |
| 4895 | Certificate Services published the CA document to Active Directory Domain Services. |
| 4896 | One or more rows have been deleted from the certificate database. |
| 4897 | Function separation enabled. |
| 4898 | Document Services loaded a template. |
| 4899 | A Certificate Services template was updated. |
| 4900 | Certificate Services template security was updated. |
Awarding Generated
The Application Generated subcategory provides a way for applications to study audit events to the Security log and is related to Authorization Manager.
| Event ID | Championship |
| 4665 | An attempt was made to create an application client context. |
| 4666 | An application attempted an operation. |
| 4667 | An application customer context was deleted. |
| 4668 | An application was initialized. |
File Share
Windows logs event ID 5140, the sole effect in the File Share subcategory, the get-go time you admission a given network share during a given logon session. This event records the share name. Be aware that Windows Server logs off network logon sessions fifty-fifty sooner than past versions of Windows do. When a user closes all open files on a server, the server seems to immediately log off the user. To correlate events, this event provides the logon ID, IP address, and username.
| Event ID | Title |
| 5140 | A network share object was accessed. |
Filtering Platform Packet Drop and Filtering Platform Connection
The Filtering Platform Packet Drop and Filtering Platform Connection subcategories log events associated with packets and network connections that are permitted or blocked by Windows Firewall and the lower-level Windows Filtering Platform. Windows Filtering Platform subcategory appeared in Windows 2008. Nosotros aren't sure why these events are logged under the Object Access category; mayhap considering Windows Filtering Platform actually audits system services rather than network-level services.
Filtering Platform Parcel Driblet events
| Result ID | Title |
| 5152 | The Windows Filtering Platform blocked a packet. |
| 5153 | A more than restrictive Windows Filtering Platform filter has blocked a packet. |
Filtering Platform Connectedness events
| Effect ID | Title |
| 5031 | The Windows Firewall Service blocked an application from accepting incoming connections on the network. |
| 5154 | The Windows Filtering Platform has permitted an application or service to heed on a port for incoming connections. |
| 5155 | The Windows Filtering Platform has blocked an application or service from listening on a port for incoming connections. |
| 5156 | The Windows Filtering Platform has immune a connection. |
| 5157 | The Windows Filtering Platform has blocked a connection. |
| 5158 | The Windows Filtering Platform has permitted a bind to a local port. |
| 5159 | The Windows Filtering Platform has blocked a bind to a local port. |
Other Object Admission Events
The Other Object Access Events subcategory is a hodgepodge of miscellaneous Object Access events. The most valuable events in this category are the ones that let you to monitor changes to scheduled tasks and file deletion.
| Upshot ID | Championship |
| 4656 | A handle to an object was requested. |
| 4658 | The handle to an object was closed. |
| 4659 | A handle to an object was requested with intent to delete. |
| 4660 | An object was deleted. |
| 4663 | An effort was made to admission an object. |
| 4664 | An attempt was made to create a difficult link. |
| 4691 | Indirect access to an object was requested. |
| 4698 | A scheduled task was created. |
| 4699 | A scheduled task was deleted. |
| 4700 | A scheduled task was enabled. |
| 4701 | A scheduled task was disabled. |
| 4702 | A scheduled task was updated. |
Bottom Line
Have a program. As mentioned earlier in this affiliate, simply auditing everything, for every access and for everyone, will brand a organisation grind to a halt. Instead, utilise a targeted approach. Think nearly the most important objects you have and which access you are looking for. Then, begin selectively auditing objects. How will the result be used? Is it just for historical purposes, or do you want to take action as before long an result occurs? The possibilities are endless. As with any powerful tool, object auditing can accomplish a great deal if it is advisedly understood and controlled.
Source: https://www.ultimatewindowssecurity.com/securitylog/book/page.aspx?spid=chapter7
0 Response to "What Type of Access Control List Defines the Settings for Auditing Access to an Object?"
Post a Comment